Its Day 80 of my 100 Days of Cloud journey, and todays post is taking a quick look at how to administer your Microsoft 365 tenancy.
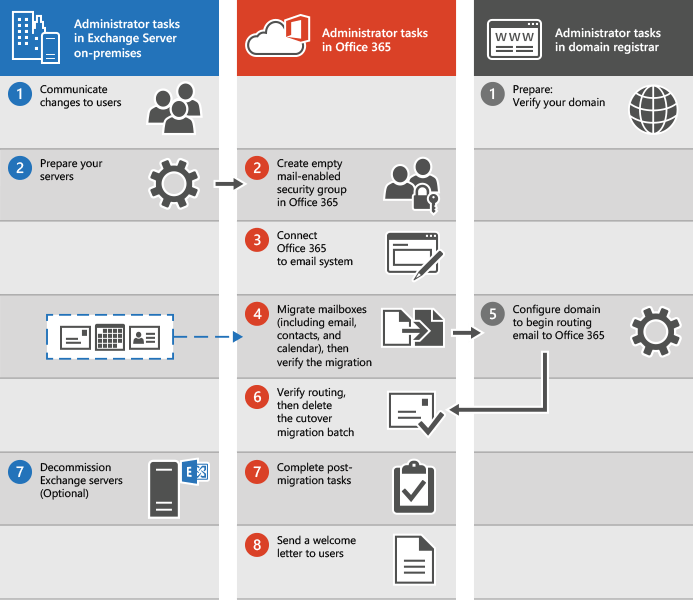
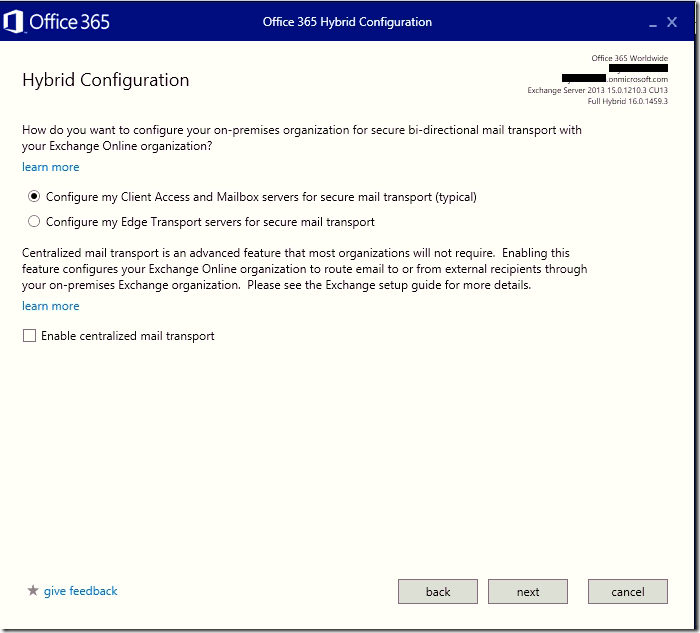
Over the previous posts, we’ve looked at how to migrate our users from our on-premises environment into Microsoft 365, and along the way we’ve chosen identity models and a suitable licensing model for our organisation.
So thats it, the hard work is done! Time for a coffee, put the feet up and read the news. Maybe do the crossword, or even todays Wordle…..
Not so fast. You now have your users in Microsoft 365, you need to manage and administer your environment. Don’t forget that Microsoft 365 is a SaaS service, so you still need to manage it using Microsoft 365 Admin Center.
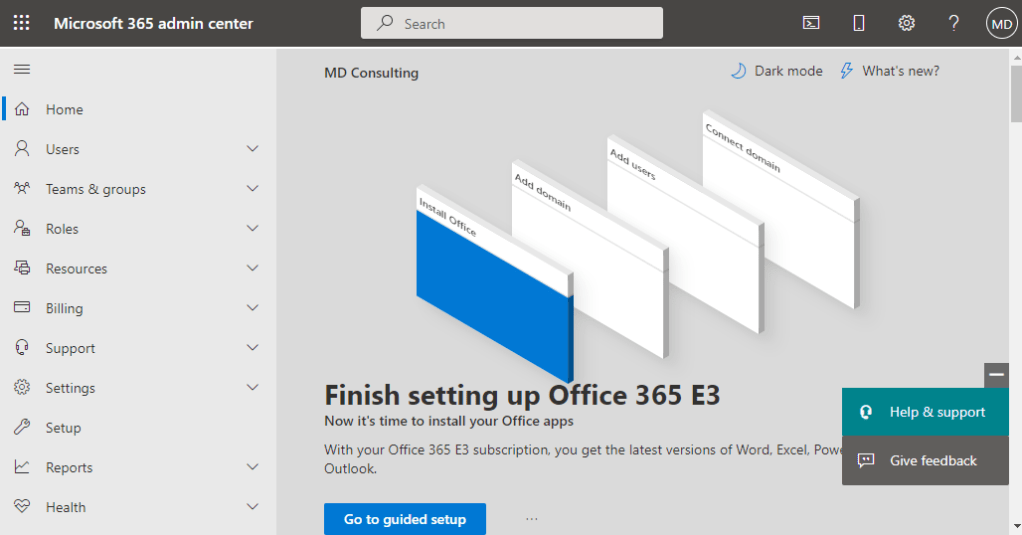
Admin Center overview
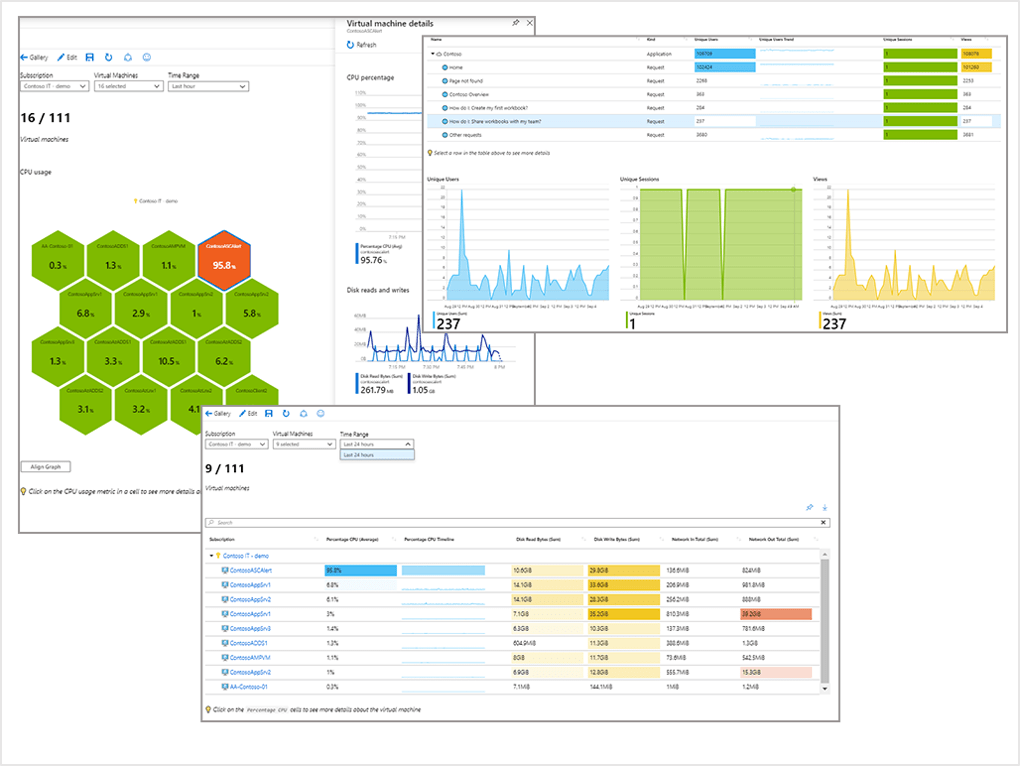
The admin center can be used to manage user accounts and mailboxes, configure the Office 365 cloud environment, monitor statistics, and so on.
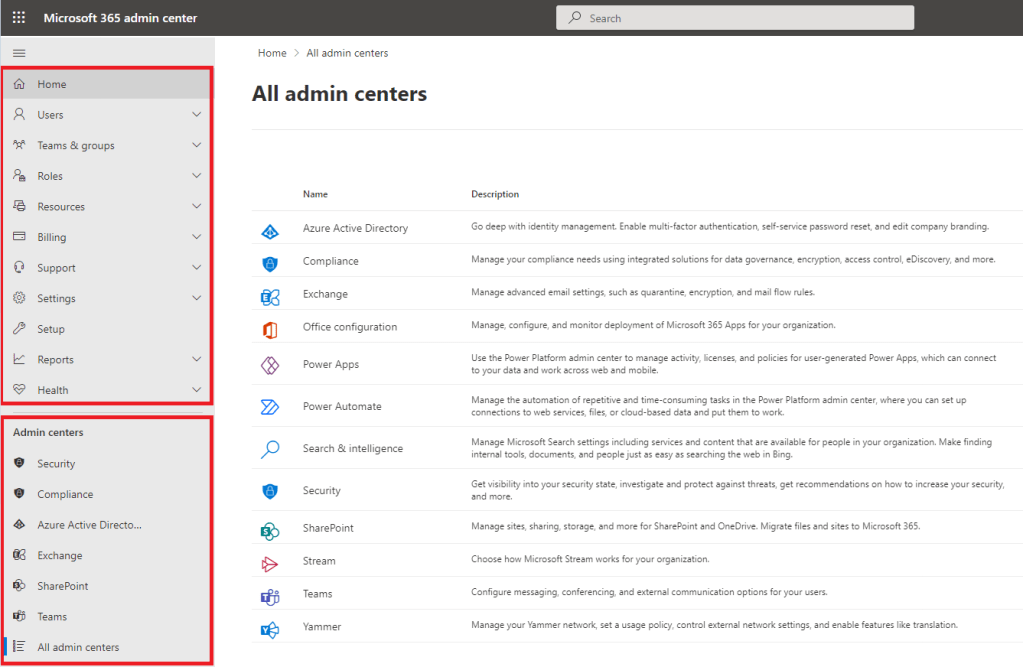
When you log on to the Admin Center, there are 2 main panels down the left hand side:
- Tenant and User Management panel – this is where you will manage the following:
- Users – the most common task for administrators is managing user accounts. You can perform tasks such as manage users (add, edit, delete, export users), reset passwords, assign or remove user licenses.
- Groups – manage Office 365 groups, security groups, distribution lists and shared mailboxes in your organization. You will also see groups that have been synchronized from our on-premises environment.
- Roles – when you sign up for a Microsoft 365 trial, the user who you sign up up with becomes a Global Admin and has full access over all aspects of the tenant. Roles allows you to assign different admin roles for other users (administrators). This is useful if you want to delegate some authority to other administrators who should be focused on Exchange management, license management or SharePoint management, without giving those users the full Global Admin role.
- Resources – allows you to create and manage resources, such as SharePoint sites and conference rooms for conference purposes.
- Billing – view your subscription status, purchase additional Microsoft cloud services, check billing and payments, and configure payment methods.
- Support – allows you to create support requests to Microsoft if needed and view recent service requests and their status.
- Settings – allows you to manage global settings including authentication settings, email settings, calendar, external sharing, password policy, Azure Active Directory integration.
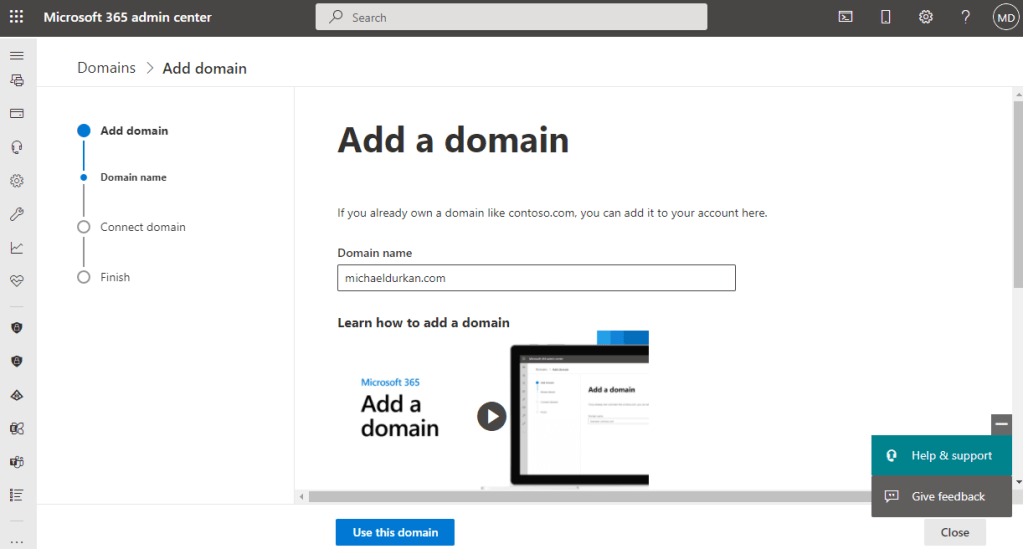
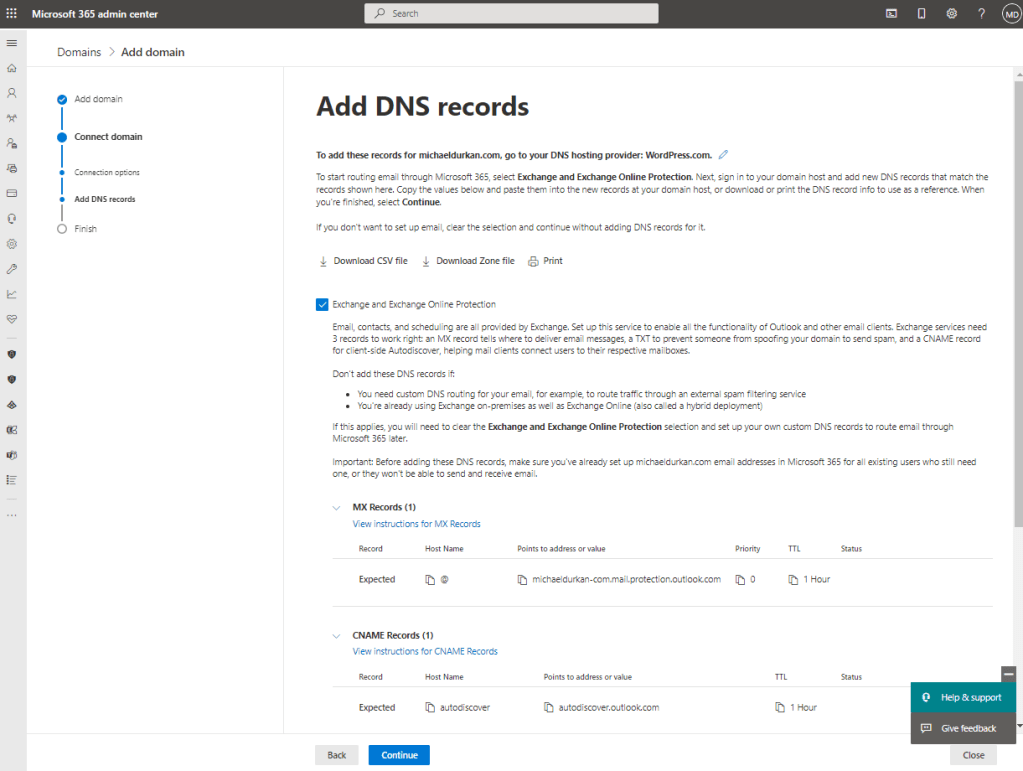
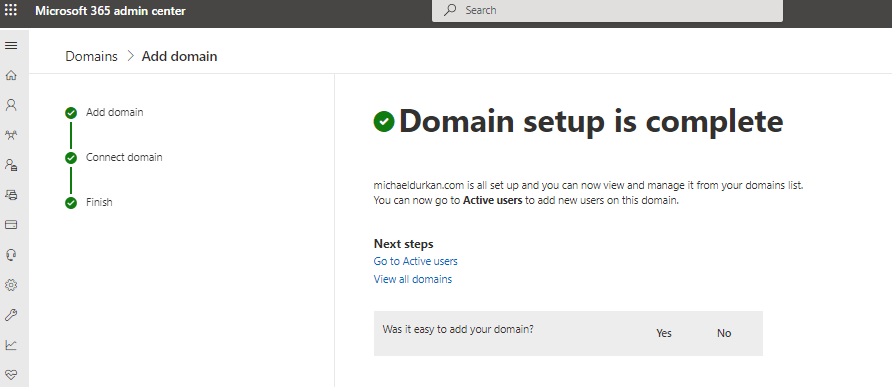
- Setup – details for your subscription, assign or manage software licenses, manage domains and data migration.
- Reports – gives detailed reports showing how users inside your company use Microsoft 365 applications. You can monitor which applications are favorite among users and compare dynamics for the selected period (7, 30, 90 or 180 days).
- Health – used to check the health of your Office 365 services.
- Admin Centers panel – this is where you will access the individual Admin centers for each of the Microsoft 365 services in your tenancy, including:
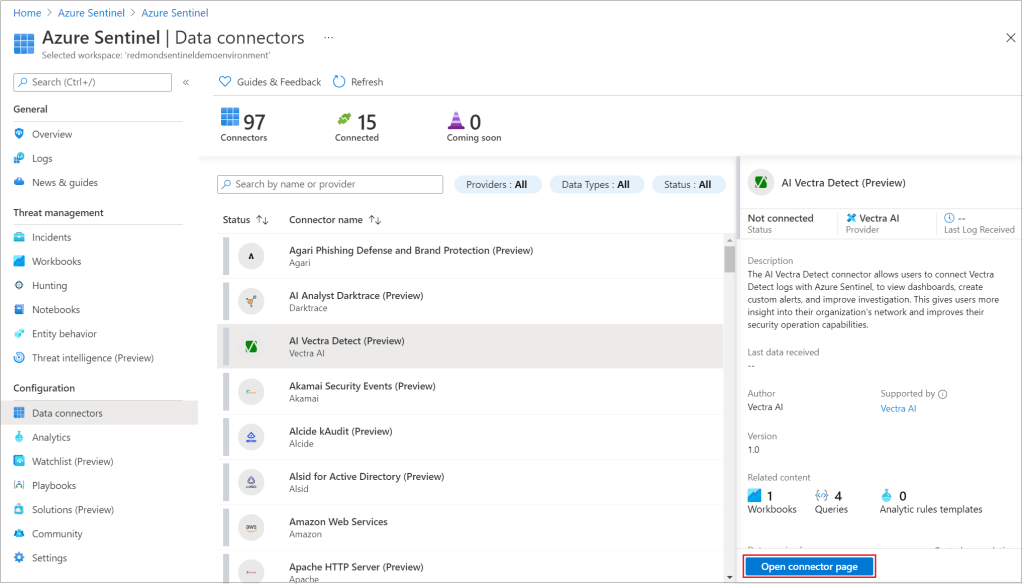
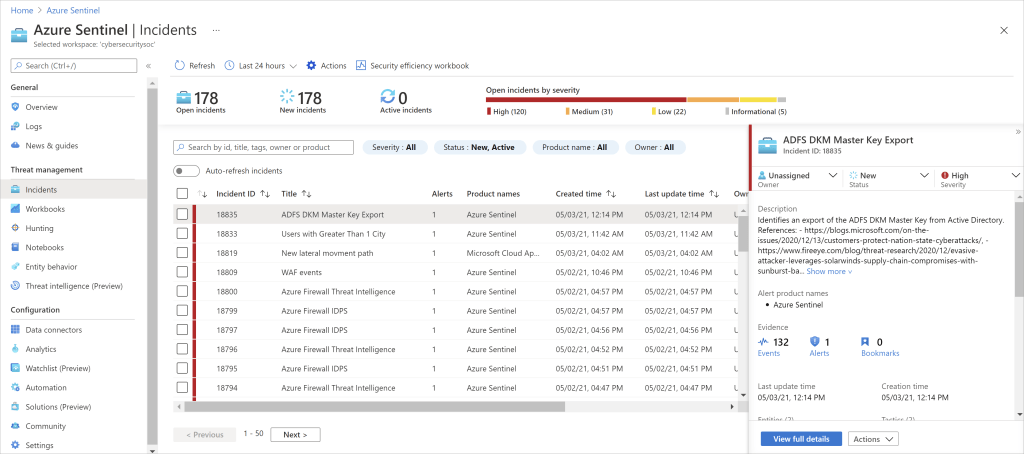
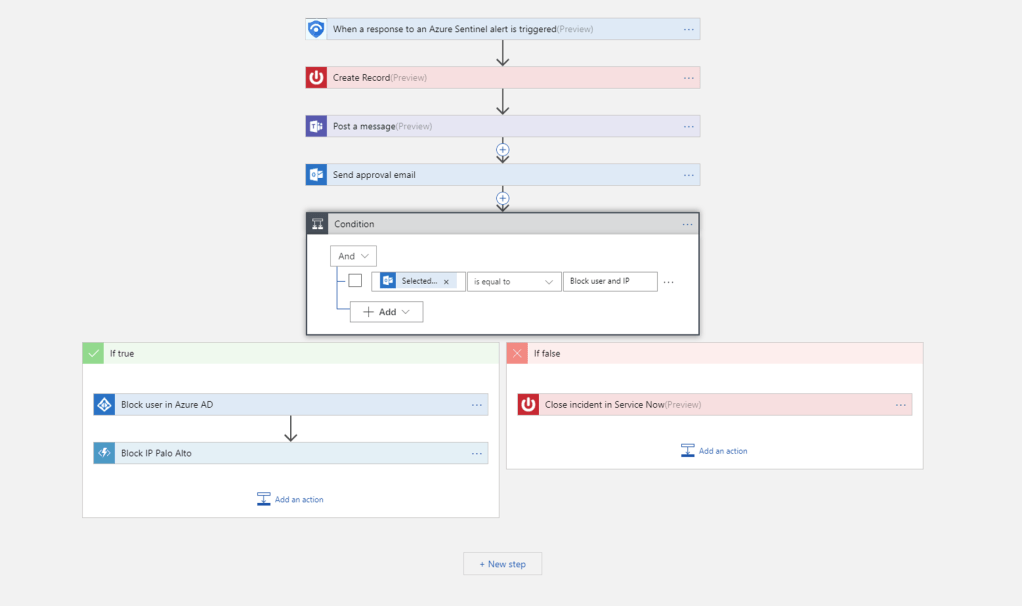
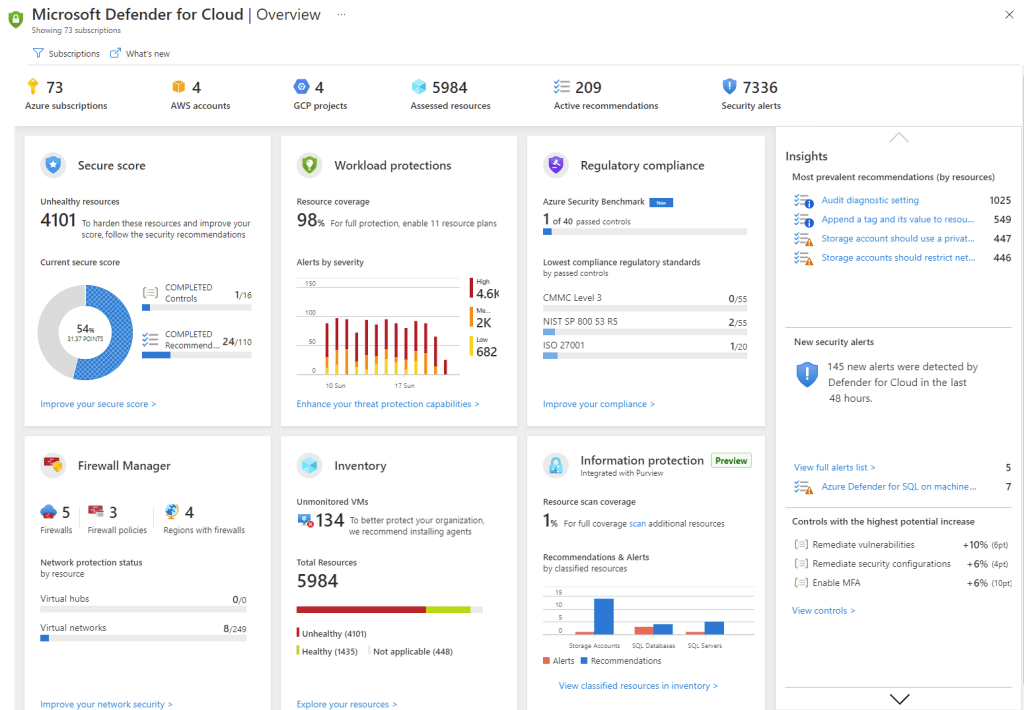
- Security – Get visibility into your security state, investigate and protect against threats, get recommendations on how to increase your security, and more.
- Compliance – Manage your compliance needs using integrated solutions for data governance, encryption, access control, eDiscovery, and more.
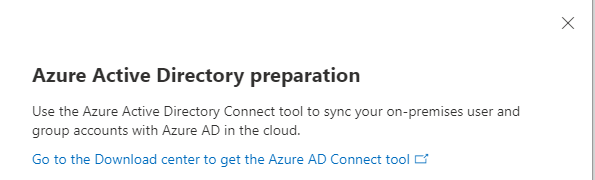
- Azure Active Directory – Allows you to configure Azure AD for Office 365 and synchronization with Windows Server Active Directory; to manage users, groups and policies; and to set access parameters for third-party applications that interact with Office 365 via Microsoft APIs.
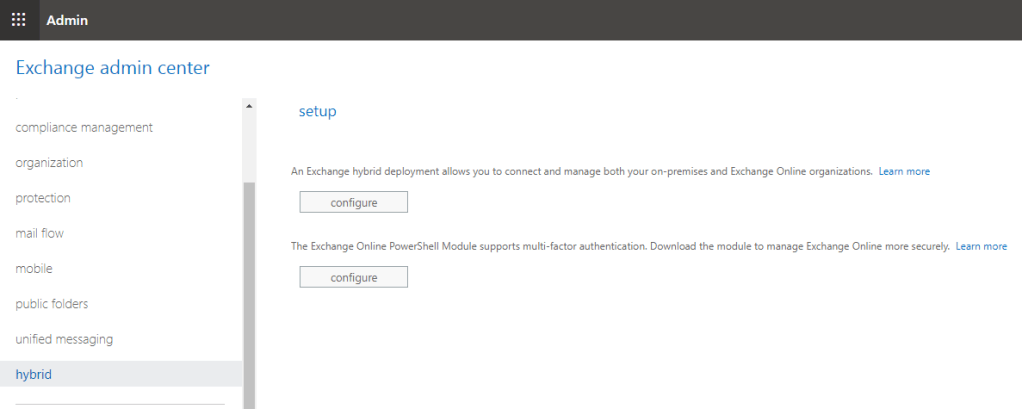
- Exchange – manage Office 365 user accounts and mailboxes. Configure group mailboxes, anti-spam protection, mail flow rules, and so on.
- SharePoint – configure the Microsoft cloud environment so that users in the organization can collaborate.
- Teams – allows you to schedule meetings for teams by using Skype for business, manage teams, set policies, view reports, and so on.
- All admin centers – Opens a page with a full list of Office 365 admin centers, including admin centers for OneDrive, Yammer Enterprise, Dynamics 365, Power Apps, Skype for business, and other services.

So what happens next?
The answer to that is really up to your organisation and how you want to benefit from the range of services available in Microsoft 365. As I’ve stated previously, the main reason why companies migrate their workloads is to remove the overhead of managing and maintaining an on-premises Exchange environment, and the underlying Operating Systems, Storage, Networking, Security and Patch Management that goes along with it.
Of course, how you develop and use these services this depends on what licensing level you have chosen (and if you missed that, take a look back at Day 78), but effectively the main options that organisations will end up using are:
- Teams – this allows instant messaging, user-to-user voice calling, team collaboration and file repostories (backed by SharePoint), and an optional full VOIP service where you can migrate your PABX to Teams Voice.
- SharePoint – we looked at this on Day 72 where we compared migrating file data to SharePoint or Azure Files.
- Azure Active Directory – this allows conditional acces and multi-factor authentication to be built into your tenant identify, as we looked at on Day 56.
Conclusion
And thats a quick look at the different options available in the Microsoft 365 admin center.
There is lots of great information out there on Microsoft 365 that goes into far more detail that I have, and a great startng point is Microsoft Docs here.
If you want to follow someone in the community to get a full overview of Microsoft/Office365 and all of the services and updates, there is no one better than Tony Redmond, who you can follow on Twitter here or you can read his updates on Petri.com here. He’s also the principal author of Office 365 for IT Pros books and blog.
Hope you enjoyed this post, until next time!